Scenario No. 1: Imagine you managed to book an appointment one month ago with your local healthcare provider to make a spirometry, thus a breathing test. Suddenly you get a message saying that your appointment is cancelled due to a cyberattack on the providers’ software system. Unfortunately, it is not an imaginary story, it is true. In early March 2023, Hospital Clínic de Barcelona experienced a ransomware attack that forced thousands of appointments to be cancelled. Hundreds of non-urgent operations and 3.000 checkups were cancelled because staff could not access the medical records of patients.
Scenario No. 2: Imagine that you wear a cardiac pacemaker and you make your regular check-ups every 6 months. The hospital maintains records of your situation and based on this information, doctors make decisions about your condition. Suddenly, a ransomware attack that targets the software operating system of the hospital manages to encrypt all hospital data, and hackers demand a ransom payment in Bitcoin cryptocurrency! Again, this is not imaginary! It is true and it occurred in May 2017, when an attack named “WannaCry” targeted computer systems worldwide.
The health sector is a goldmine of data and as medical devices come into our lives and healthcare with such an urge, then unfortunately, malicious hacking groups will progressively exploit the gap in security systems to unleash their attacks.
The 3rd most attacked sector
The healthcare sector is a common target for cybercriminals. In comparison to 2021, in 2022 there was a 60% increase in attacks, or to say it differently, healthcare organizations experienced 1,426 attacks per week in 2022, according to Check Point Research. The cost of this data breach for a healthcare organisation is very high. Over the past two years, this cost grew by 42%, while each incident alone costs $10.10 million on average.
In the USA, from 2016 to 2021, cyberattacks on hospitals and health systems doubled, according to the Journal of the American Medical Association. Globally, there was an average of 1,684 attacks per week in 2022– a year-on-year increase of 22%.
For the first quarter of 2023, the healthcare sector dropped to the 5th position globally in the cyberattack index of CheckPoint Research.
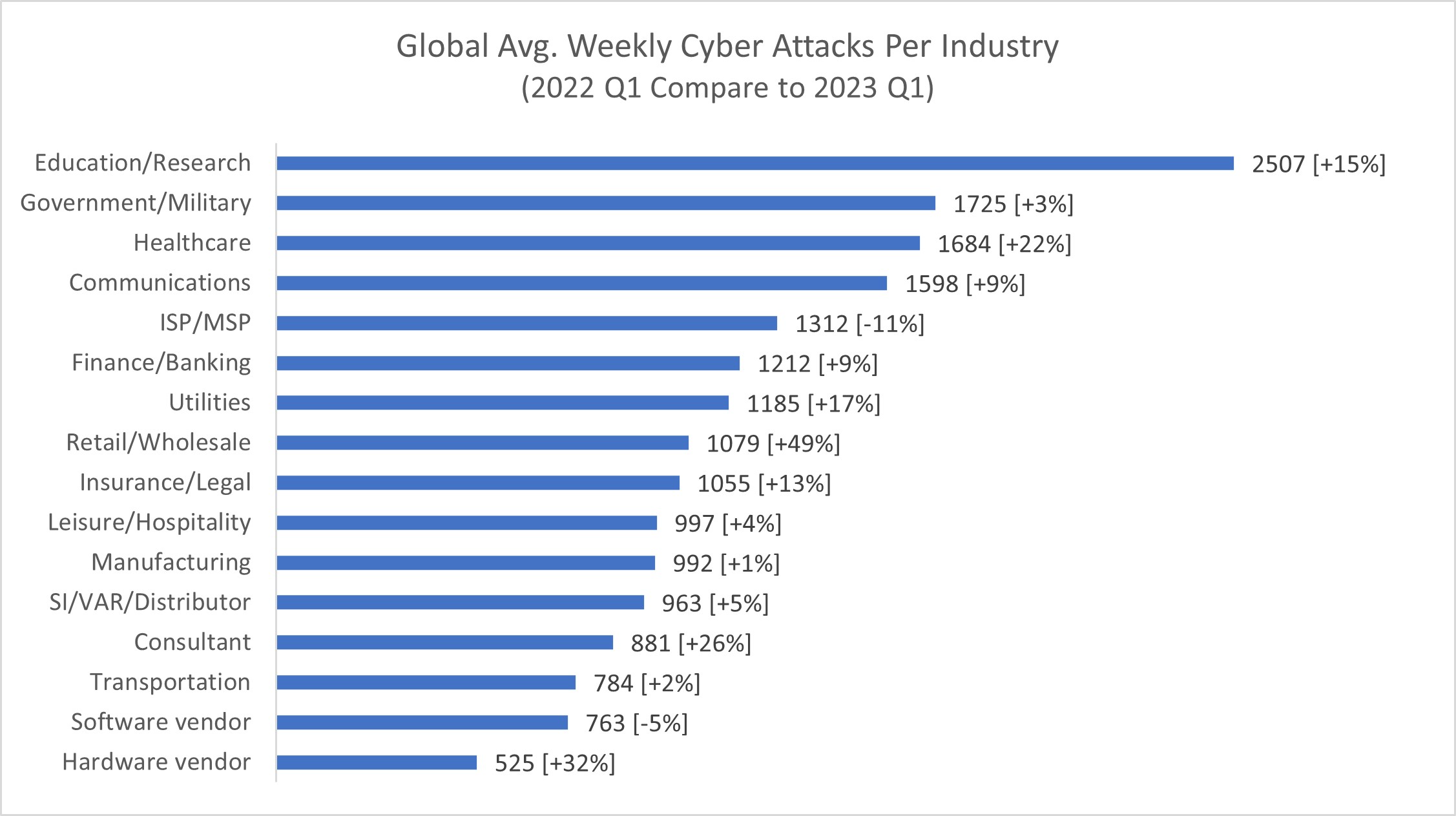
Cyberattacks per industry- 2022, CheckPoint Research
But why the hospitals?
One could try to think of the motives for these immoral attacks that can potentially harm people’s lives. Except for the immoral incentives of these malicious hackers, like the pride they take in their acts, the “show-off” and the competition amongst them, there is always the economic reason behind them. As in the 2017 “WannaCry” attack, hackers can demand ransom to give back the data of the patients to the hospitals.
Another reason for these frequent attacks is the vulnerability of the system. As medical staff has been trying to cope with the Covid-19 pandemic, tiredness often caused mistakes and mismanagement in the security field of medical devices. People did not have the time or the courage to cope with complex security issues while they were daily struggling with their patients.
What’s more, hospitals and other providers are often managed through easily exploited legacy IT systems. A survey by the Healthcare Information and Management Systems Society found that 73% of healthcare provider organizations use costly systems that are often rife with security gaps.
A highly sensitive sector
Healthcare is not like no other sector. While hackers seem to “love” the military, government, and education sectors the most, the attacks on the healthcare sector pose an enormous risk for society, like no other – people’s lives are directly endangered.
Except for the integrity and the personal information that no one should obtain in an ideal world without a patient’s will, here we talk about lives at stake. When your scheduled operation is cancelled or the personal records of your cardiovascular problem are lost, then you are in trouble.
Different types of attacks on healthcare
As technology progresses at a high pace, so do hackers. Attacks on software systems differ in terms of magnitude, methodology, damage, and disruption caused. Let’s see the 3 most common types of cyberattacks:
Ransomware: it is one of the most favorable ways that a hospital gets attacked. Ransomware is a type of malware that infects systems and files, rendering them inaccessible until a ransom is paid. Hospitals continue working, go back to pen and pencil, slowing medical processes, while they are demanded to pay a ransom to get their files back. How do hackers infect the system? Usually by sending phishing emails containing a malicious attachment, via a user clicking on a malicious link, or by viewing an advertisement containing malware. In one case, the Hollywood Presbyterian Hospital in California was attacked, patient care was delayed and the hospital paid $17,000 to regain access to files and its network.
Data breaches: widely observed in the healthcare sector, data breaches currently have affected over 15 million health records globally. It is THE most common way to attack a hospital, by emails sent to individuals with a notification of the breach together with 2,3 years of credit and identity monitoring. Breaches can be caused by credential-stealing malware, an insider who either purposefully or accidentally discloses patient data, or lost laptops or other devices.
Distributed denial of service (DDoS) attacks: a kind of attack with often ideological motives. Popular among hacktivists but also cybercriminals, this tactic is used to overwhelm a network to the point of inoperability. In this way, medical personnel cannot have internet access, to send and receive emails, prescriptions, records, and information. A well-known example was the attack on the Boston Children’s Hospital in 2014. Then a well-known hacktivist group, that did not agree with the hospital recommendation in the custody case of a 14-year-old girl, and thus managed to conduct DDoS attacks against the hospital’s network, which resulted in others on that network, including Harvard University and all its hospitals, to lose Internet access as well.

Real-life cyberattacks
In 2023
Since the start of 2023, numerous cyberattacks affecting hospitals and healthcare organisations all over Europe have been reported. The bad news first came from the University medical center in Maastricht and the cybersecurity agency Z-CERT being hit by the pro-Russian hacker group “Killnet” which launched a DDoS attack. In February, an unknown hacker group named “Anonymous Sudan” hit the websites of nine hospitals in Denmark that were forced to shut down. Thousands of patients’ appointments in Hospital Clínic de Barcelona, Spain were cancelled in March due to a ransomware attack. In the same month, the Centre Hospitalier Universitaire Saint-Pierre in Brussels was targeted. And the list goes on. In the UK, due to the numerous ransomware attacks on the NHS in recent years, the government published its new cybersecurity strategy for the National Health Service intending to make it highly resistant to cyber assaults no later than 2030.
WannaCry
Another major attack, this time on a global scale was the infamous “WannaCry” that hit computers running Windows. Most Windows users had not managed to update their systems with a recent official security patch, so their software was out-of-date versions of Windows and became vulnerable to large-scale attacks. The WannaCry demanded a ransom of initially $300 worth of Bitcoin, later $600 worth. It infected an estimated 230,000 computers across 150 countries in just a few hours.
Stolen patients’ personal data
Just a year ago, in 2022, Shields Health Care Group in Massachusetts, USA, was hit by a cybercriminal who had gained unauthorized access to some of its IT systems. As a result, over 2 million patients had their Protected Health Information stolen, including names, addresses, Social Security numbers, insurance information, and medical history information.

ENTRUST Kick-Off Meeting in Athens, Greece
Why do we need projects like ENTRUST?
In an effort to tackle this major issue of cybersecurity, the European Union covers the funding for research programmes and collaborative projects that will offer revolutionary solutions and innovations.
One of these projects is ENTRUST, a Horizon-funded (GA No. 101095634) Research, and Innovation Action that will secure connected medical devices against cyber threats. Future Needs is a partner in the project, leading the Dissemination, Communication, Exploitation, and Impact Creation work package. Furthermore, Future Needs leads the tasks for Data Management, Legal and Ethical Compliance of the project, and the task Shaping of the Ethical & Legal Dimension of Trust Management in Next-Generation of smart connected medical devices which will conduct an ethical analysis.
ENTRUST brings together 20 academic and industrial partners from 13 countries, spanning the period from January 2023 to December 2025. The project envisions holistically managing the lifecycle of connected medical devices, strengthening trust in the entire medical ecosystem. It leverages a series of breakthrough solutions to enhance assurance without limiting the applicability of connected medical devices. This includes formally verified trust models, remote attestation mechanisms, risk assessment processes, secure lifecycle procedures, security policies, technical recommendations, and real-time conformity certificates based on distributed ledgers.
The use cases of ENTRUST
The added value and effectiveness of ENTRUST will be validated and evaluated in four real-world use cases ranging from wearable and medical devices used for remote patient monitoring to high-end stationary equipment used in hospitals and clinics.
Dynamic Trust Assessment in ECG Monitoring Portable Devices and Complex Stationary Devices in a Hospital Setting: This use case will be carried out in the Ankara University Hospital, coordinated by Kardinero, a leading CMD manufacturer in Turkey. Its scope is to validate ENTRUST’s security mechanisms and trust assessment over Bluetooth Low Energy (BLE) communication, also considering a collaborative fleet of CMDs.
Ambient Intelligent System for Supporting Independent and Safe Living: Here ENTRUST will enhance the security posture of remote patients through Verifiable Credentials depicting the operational state per device under a hierarchical SoS environment. This use case will take place in Norway, where Tellu is one of the major digital health providers providing personal healthcare gateways at patients’ homes and other healthcare facilities.
Digital Assistance Towards Enhancing the Health and Well-being of Patients and Carers: Two hospitals are involved in this use case, POLARIS’s hospital in Romania and in the Hospital do Espírito Santo de Évora in Portugal. This use case will focus on ENTRUST’s trust framework and secure data exchange and how it can support the integration of CMDs in the hospital’s IT infrastructure, as well as the remote monitoring and maintenance of legacy devices and equipment.


